- Knowledge Base
- General
- Control your Office 365 users’ password policies
Article sections
| Summary: | This article takes you through the steps on how to control your Office 365 users’ password policies |
| Article Type: | Information for IT Admin role |
| Related Product(s): | This article relates to the following products:
|
| Related Articles: |
|
How to control Office 365 users’ password policies
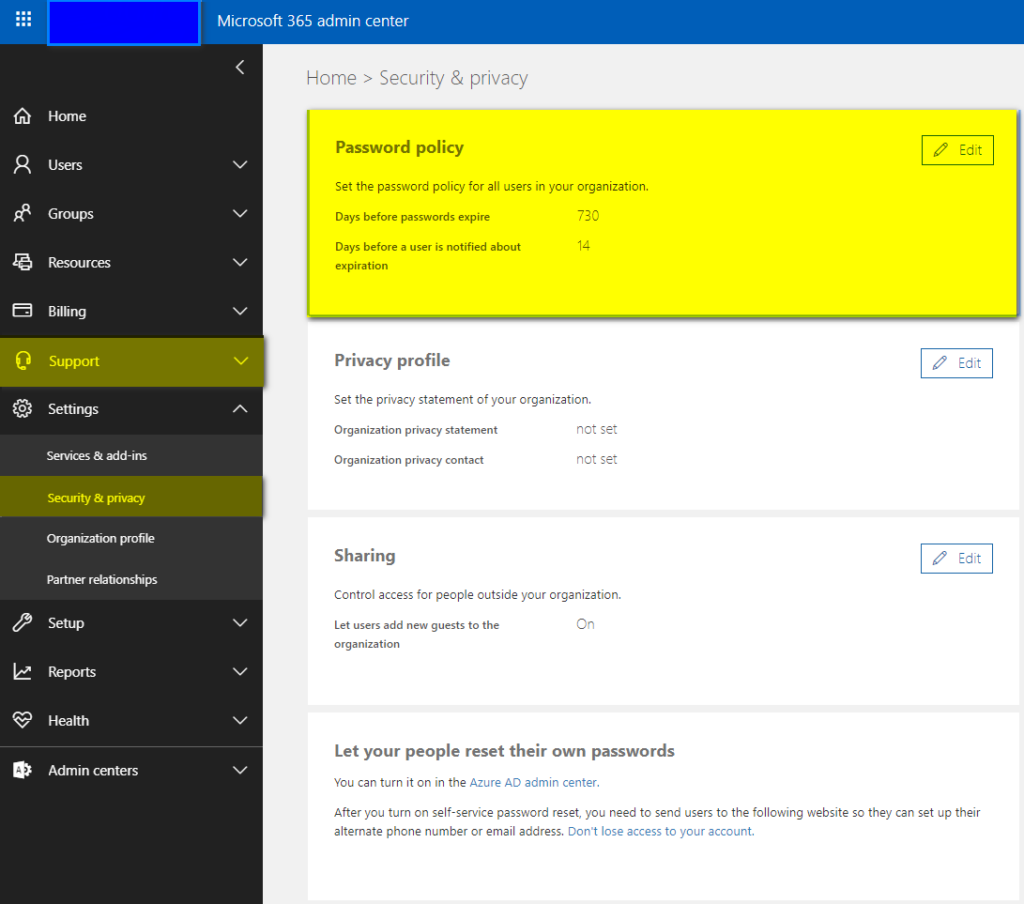
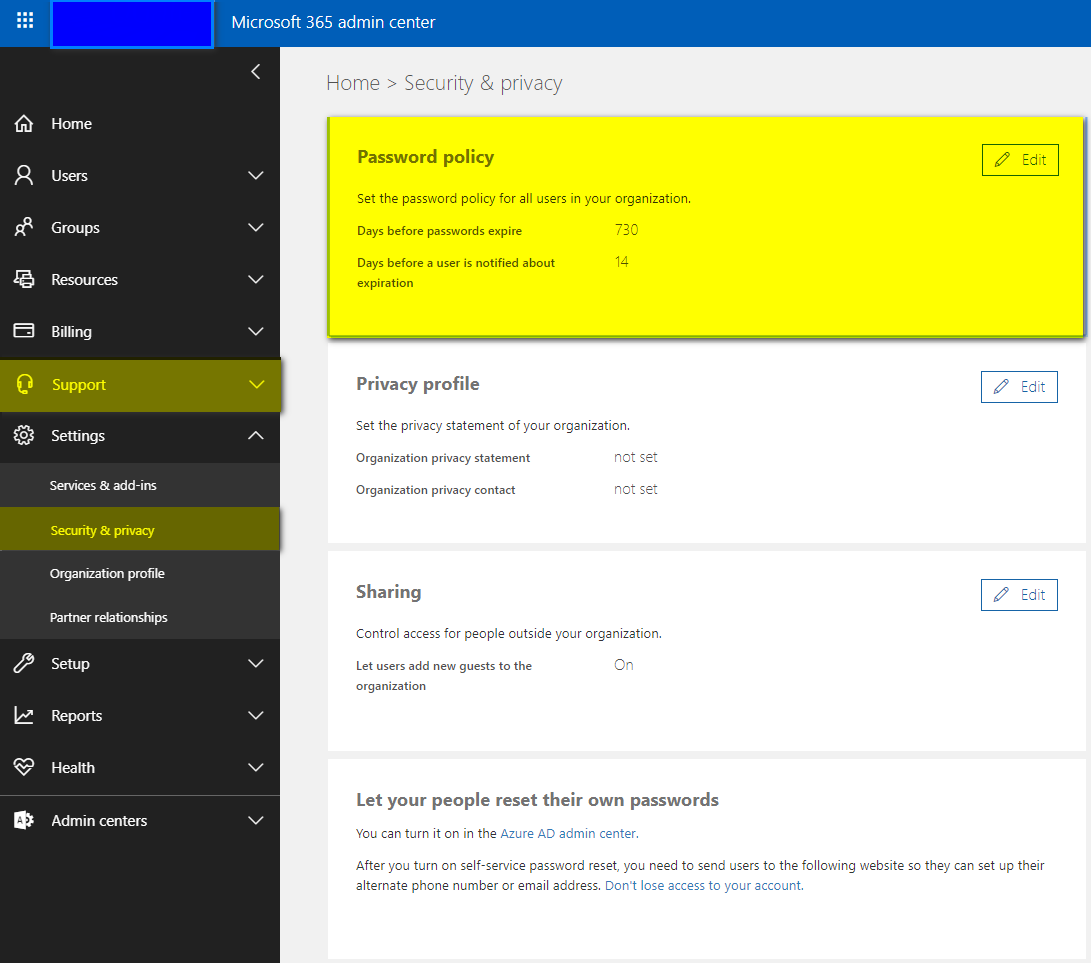
Within Office 365 Admin Portal you have the ability to control the Global Password Policy for users; this allows you to select whether passwords expire, the days before passwords expire and the days before a user is notified about expiration. You can reach the settings by following the next image.
Setting a Global Password Policy is great for security and inhouse processes however there may be times where you really need a user to be excluded from the Global Policy; this is not something that Microsoft will allow you to do without the use of an external tool. One scenario where you may want to ensure a User or Non-Interactive user retains its password is when it is being utilised as a connector for a solution, if the Password expires then the connection will be disrupted which some or all of the solution will not be working.
The process for disabling expiration of a password for a single user is defined as the following:
- Ensure you have installed the Azure AD PowerShell Module from here.
- Using your company administrator credentials, connect to Windows PowerShell
- Execute the following command:
“Set -MsolUser -UserPrincipalName <user ID> -PasswordNeverExpires $true
This will set the users Password to never expire, the warning that comes with this is that the age of the password still exists and will still count each day. This means that should you reenable expiration at 90 days, any password that is 90 or more days old, will have a password reset enforcement.
If you are looking to find out the status of all users to find out whether their passwords are set to expire or not, you have use the following command:
“Get-MSOLUser | Select UserPrincipalName, PasswordNeverExpires”
For more commands and further information, the full Microsoft Support article and source of this KB can be found at here.
Related Articles
- How does Power BI Licensing work?
- Understanding Date Fields in the Dataverse
- Power BI URL Filtering
- Create Custom Reusable Controls in PowerApps
- Microsoft Flow FAQ
- Creating Microsoft Dynamics 365 Workflows Tips
- How to: Creating a "Run Once" Daily Trigger using Power Automate
- How-to: Microsoft Dynamics 365 System Backups
- How to check your Microsoft storage use
- Modifying Silently in Dynamics 365